Download Profiles On Iphone

Device profiles OverDrive's device profiles are designed to give you a snapshot of how popular devices can be used with digital titles from OverDrive-powered library. TheTruthSpy: Mobile Spy - Android Spy - Hidden Spy App - Phone Tracker. Include more 25+ features such as: GPS, SMS, Call Recorder, WhatsApp, Live Audio and More.
What is a Configuration Profile? Configuration profiles are created with Apple’s iPhone Configuration Utility. They’re intended for IT departments and cellular carriers. These files have the.mobileconfig file extension and are essentially an easy way of distributing network settings to iOS devices. For example, a configuration profile can contain Wi-Fi, VPN, email, calendar, and even passcode restriction settings. An IT department can distribute the configuration profile to its employees, allowing them to quickly configure their device to connect to the corporate network and other services.
A cellular carrier could distribute a configuration profile file containing its access point name (APN) settings, allowing users to easily configure cellular data settings on their device without having to enter all the information manually. So far, so good.
However, a malicious person could theoretically create their own configuration profile files and distribute them. Dodge 2005 Durango Repair Manual. The profile could configure the device to use a malicious proxy or, effectively allowing the attacker to monitor everything going over the network and redirect the device to phishing websites or malicious pages. Configuration profiles could also be used to install certificates. If a malicious certificate was installed, the attacker could effectively impersonate secure websites like banks. How Configuration Profiles Could Be Installed Configuration profiles can be distributed in several different ways.
The most concerning ways are as email attachments and as files on web pages. An attacker could create a phishing email (probably a targeted email) encouraging employees of a corporation to install a malicious configuration profile attached to the email. Or, an attacker could set up a phishing site that tries to download a configuration profile file. When the configuration profile is downloaded, iOS will display information about the contents of the profile and ask you if you want to install it.
You’re only at risk if you choose to download and install a malicious configuration profile. Of course, many computers in the real world are infected because users agree to download and run malicious files. The configuration profile can only infect the device in a limited way. It can’t replicate itself like a, nor can it hide itself from view like a rootkit. It can only point the device at malicious servers and install malicious certificates. If the configuration profile is removed, the harmful changes will be erased.
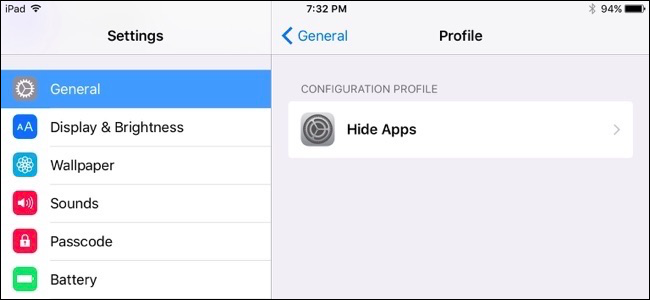
Managing Installed Configuration Profiles You can see if you have any configuration profiles installed by opening the Settings app on your iPhone, iPad, or iPod Touch and tapping the General category. Look for the Profile option near the bottom of the list.
If you don’t see it on the General pane, you don’t have any configuration profiles installed. If you do see the option, you can tap it to view your installed configuration profiles, inspect them, and remove any you don’t need. Enterprises using managed iOS devices can prevent users from installing additional configuration profiles on their devices. Enterprises can also query their managed devices to see if they have additional configuration profiles installed and remove them remotely if needed. Enterprises using managed iOS devices have a way to ensure those devices aren’t infected by malicious configuration profiles. This is more of a theoretical vulnerability, as we’re not aware of anyone actively exploiting it.
Still, it demonstrates that. You should exercise caution when downloading and installing potentially harmful things, whether they’re executable programs on Windows or configuration profiles on iOS.